
Security testing is becoming a crucial part of software development. This post covers the fundamental techniques and tools that software developers can rely on.
With cyberattacks on the news seemingly every day these past few years, and software driving everything from fridges to autonomous cars, it’s no wonder why cybersecurity is becoming a critical concern for product developers. In this post, we’ll attempt to cover the basics of security testing, its various types, and some of the most popular security testing tools that you can use to ensure the security of your software products.
What is security testing?
In general, the goal of security testing is to evaluate the security of a software system, identifying any weaknesses and vulnerabilities to ensure that data and resources are safe from unauthorized access by intruders, data breaches, and other security-related incidents.
Thorough security testing can help reduce the chance of vulnerabilities making it into the final end product. It is a type of non-functional testing, meaning that it doesn’t test the core of “what” the software application does, but rather “how” it performs those functions to see whether safety and reliability are up to scratch.
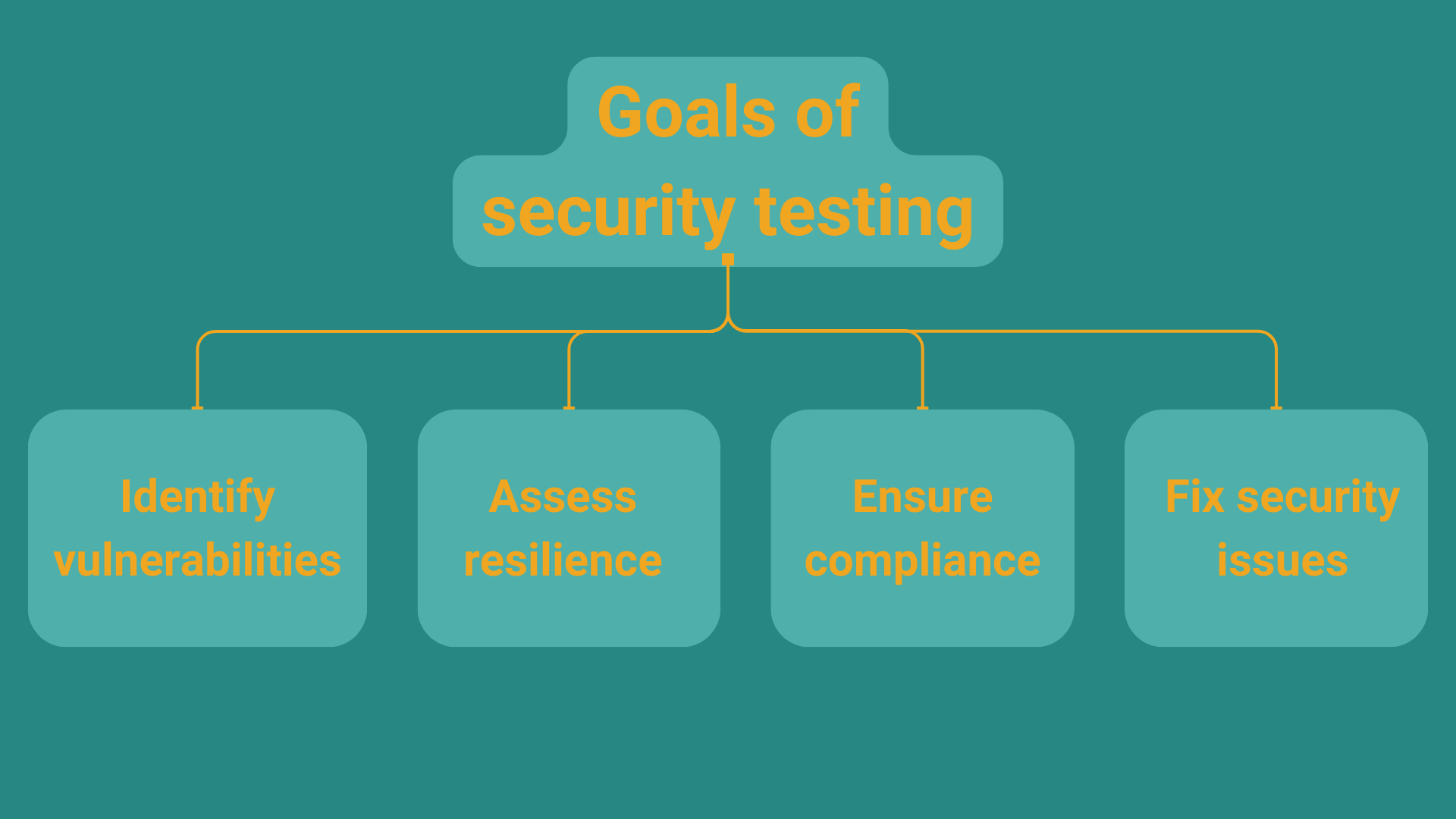
The key goals of security testing are to:
- Identify all possible security vulnerabilities so that developers can fix them
- Evaluate the system’s resilience against attacks
- Ensure compliance with security standards or legal requirements
- Fix security issues before deployment to production
An added benefit of security testing is that it can help an organization better understand security threats, which supports the company in preparing for incidents.
The principles of security testing
Any security testing activities should be based on a set of fundamental principles. These six principles govern all security testing processes and provide a foundation for the goals and techniques used for security testing:
- Confidentiality: Access to sensitive information should be limited.
- Integrity: Data should be consistent, accurate, and trusted not to have been modified by unauthorized intruders.
- Availability: Critical systems or data should always be available to the users that need to use them.
- Authentication: A mechanism for verifying the identity of anyone accessing sensitive systems or data should protect the system.
- Authorization: Access control for authenticated users based on their roles or permissions should be implemented.
- Non-repudiation: Digital signatures (authentication) and timestamps should be in place to ensure the safety of data exchange between connected systems
What are the main types of security testing?
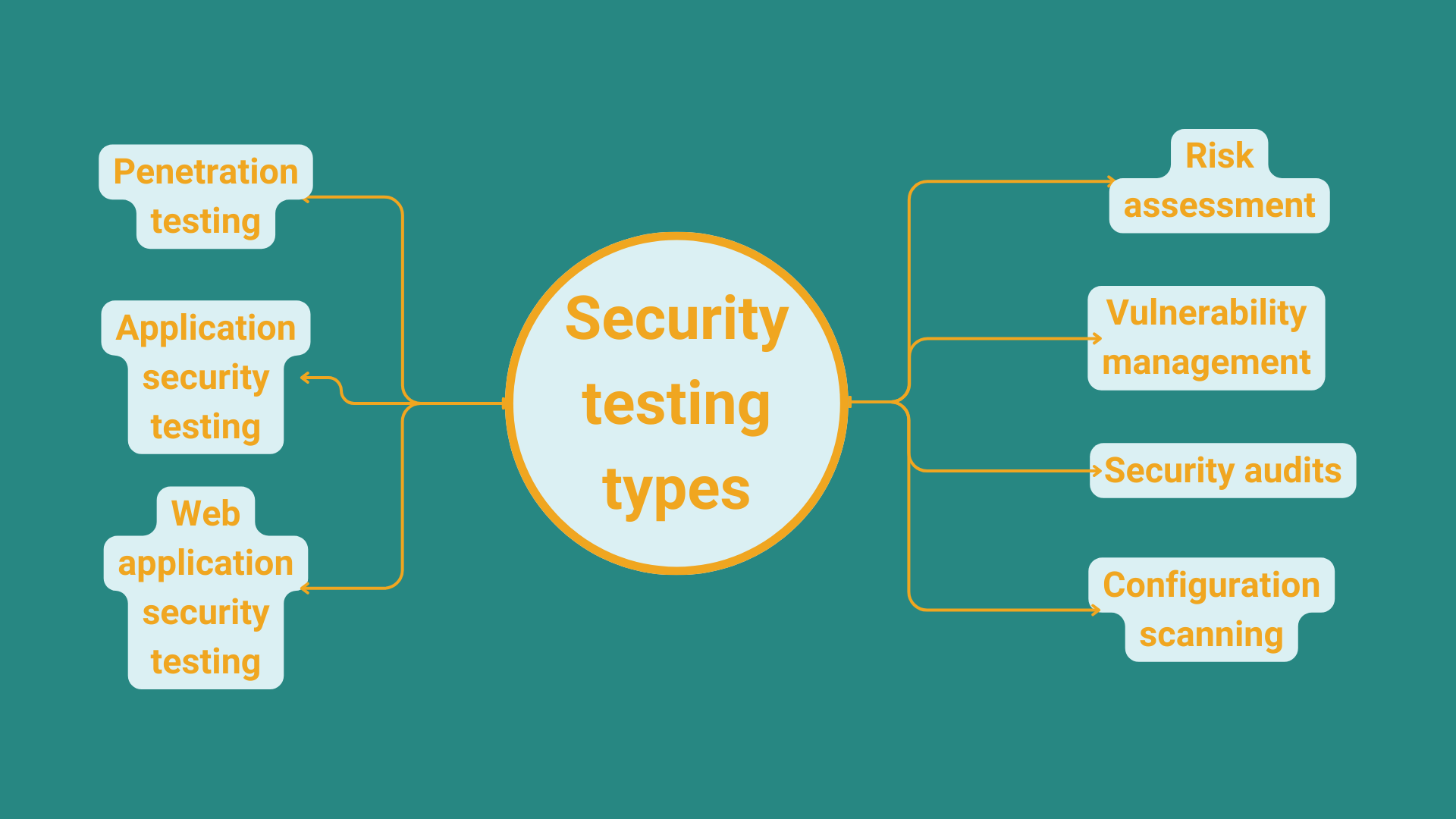
Security testing is a broad concept that encompasses a variety of strategies, techniques, processes, and frameworks. However, in the context of software security testing, we generally distinguish between the following types of security testing:
- Penetration testing
- Application security testing
- Web application security testing
- Risk assessment
- Vulnerability management
- Security audits
- Configuration scanning
Penetration testing
Penetration testing can be the first step of evaluating the existing security measures of a software product. It mainly consists of simulating actual cyber attacks to see how the system holds up.
Penetration testing is also useful to find gaps in your security “armor” that have not yet been discovered. While penetration testing started as a purely manual procedure carried out by ethical hackers, today, automation plays a larger role in the penetration testing process, making it easier to discover vulnerabilities in a system.
Application Security Testing (AST)
AST is actually an umbrella term that denotes a variety of technologies that help find and get rid of vulnerabilities.
Practices like the following fall under the umbrella of AST:
- Static Application Security Testing: A type of white-box testing that aims to analyze your applications' source code while it is not running to identify vulnerabilities.
- Dynamic Application Security Testing: A black-box testing technique that works by simulating attacks on the application while it’s running.
- Interactive Application Security Testing: Often integrated in the CI/CD pipeline, IAST is used to scan the source code of your application.
- Software Composition Analysis: Used to identify external components (mostly open-source ones) in your software that can cause vulnerabilities.
- Runtime Application Self-protection: Consists of runtime monitoring to detect and prevent attacks in real time.
Web application security testing
This category encompasses forms of security testing targeted on web applications. It mainly consists of manual and automated penetration testing strategies for web applications. The goal is to make sure that existing websites are secure, and when building a new website, to ensure that adequate security controls are implemented.
The OWASP (Open Web Application Security Project) provides some great information about the topic on its website.
ℹ️ What is OWASP?
“The Open Web Application Security Project is a nonprofit foundation that works to improve the security of software. […] We are an open community dedicated to enabling organizations to conceive, develop, acquire, operate, and maintain applications that can be trusted. All of our projects, tools, documents, forums, and chapters are free and open to anyone interested in improving application security.” Source: https://owasp.org
API security testing
Lots more software being embedded in a variety of products means a huge number of application programming interfaces (APIs) popping up all around us. It is vital that the offered APIs are not exploited by unauthorized users (hackers), letting them gain access to or manipulate sensitive data. Naturally, it makes a great deal of sense to “fortify” these parts of an application. For the sake of safety, it is crucial to strengthen the authentication of requests & authorization of users.
🎉 Testing trends 2024
API test automation is actually one of the up-and-coming trends in software testing. Find out about the key technologies and strategies that will influence software testing in 2024 and beyond!
Vulnerability scanning
Tools that automatically scan systems to detect vulnerabilities are of great help to security testing teams. Part of this process is not only to analyze the system for vulnerabilities, but also to prioritize risks (taking into account the business impact of any potential incidents) so that serious issues can be tackled first. Therefore, vulnerability scanning has a broader scope and may involve IT Operations teams or other business stakeholders.
Configuration Scanning
Misconfiguration of the system can also cause trouble. That’s why configuration scanning (aka security scanning) is used to check if the system is used in accordance with best practices to ensure security. This, of course, can also be automated, with reports provided on both misconfigurations and optimal ways to fix them.
In addition, there are also types of security testing that employ a broader scope including security audits (providing a thorough security analysis of the software), risk assessment to inform mitigation procedures, and security posture assessments to gauge the effectiveness of current security controls in place.
Security testing tools
OK, so how do you start doing security testing in practice? To help hit the ground running, here’s a list of the most common categories of security testing tools, and some open-source examples of tools that you can use for free. List by OWASP:
| Source code analysis tools | Dynamic application security testing tools for web applications | Interactive application security testing tools |
|---|---|---|
| GitHub code scanning, Contrast CodeSec - Scan & Serverless, Coverity Scan Static Analysis, HCL AppScan CodeSweep, AppSweep |
StackHawk, Arachni, VWT Digital’s sec-helpers, OWASP purpleteam, CI Fuzz CLI, Code Intelligence App |
Contrast Community Edition (CE) |
Overall, if you don’t yet have a sound security testing procedure in place, it’s highly recommended that you familiarize yourself with the techniques and tools outlined above. With cybersecurity concerns becoming more of a vital concern, security should be handled as a key factor of software quality.